A recent tweet by Dave Kennedy in response to a question about the cybersecurity job market got me thinking about the mismatch between what companies are looking for and the pool of applicants:
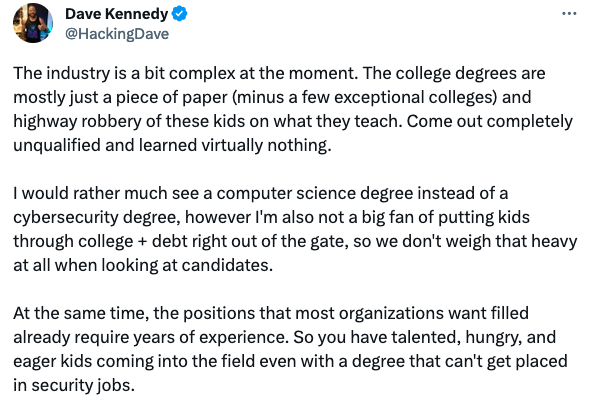
I don’t have the experience that Dave does with hiring, but I agree with the sentiment. College graduates are not always prepared for cybersecurity work (sorry!). Employers want someone they can quickly see results from, and often junior positions require mentoring.
While that reality is unfortunate for those with limited experience, there are still ways you can demonstrate worth to potential future employers if you don’t have experience in the industry.
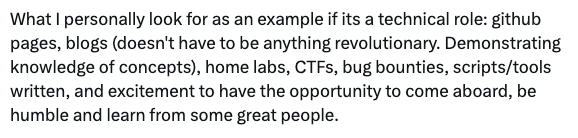
Start a blog
And keep it simple. No one expects you to write some innovative treatise on cybersecurity or disclose some hot new 0-day vulnerability. It’s fine to be new to the field and not know everything, but still share your thoughts on cybersecurity-related issues.
As a pro, you will be expected to stay on top of security-related news. You should subscribe to newsletters, check Twitter (“X”), read blogs, listen to podcasts, etc.
There are a ton of resources just a Google search away. Find an interesting tidbit on Twitter, Reddit, or wherever you get news, and expand on it. No need to overthink this! Why is it noteworthy? Add some context. Share your thoughts. Write a couple hundred words and click “publish.”
By doing this, you are demonstrating that you stay on top of the news and that you understand the material. This alone gives you an advantage over other applicants.
Write about whatever you are reading, and do so on a regular basis. Set a reminder every week and set aside an hour to write. After a couple of months, you’ll have enough entries and can include your blog on your resume.
Do I need an active Github account?
I recommend doing so, but I don’t consider it absolutely necessary. I have worked with cybersecurity engineers who don’t write code and are still great at their jobs. And others who do code but don’t contribute to projects via Github.
That said, many roles do want someone who can code, or at the very least understand how code works. There’s no better way to demonstrate that than to either upload a project of your own or contribute to an existing project. There are plenty of security tools out there that you can add to or fork and make your own.
At the very least, you should know the basics of how to pull down code from github, modify it, and run it. And if you’re having trouble finding a good contribution to make, I often find that documentation on tools needs some work. Check out that readme file that ships with the tool and see if you can contribute.
Do I need a home lab?
You should definitely know how to set up virtualized servers, and I recommend having your own home lab. A good exercise is to run a virtual server with known vulnerable software (like OWASP’s Juice Shop or DVWA). Then set up another virtual machine to act as an attacker.
There are plenty of tutorials on how to do this, and if you’re a recent grad, I hope this is an exercise you’ve done before. Even if you have your own server at home, I still recommend setting up some virtual servers in popular cloud providers like Azure or AWS just to get a feel for how those platforms work. Just be careful not to leave machines running and rack up a bill (most have a free tier)!
Final thoughts
The other suggestions Dave makes are good was well: compete in CTFs (and write up your experience!) and write tools (even basic ones). If you’re a beginner, I’d avoid worrying about bug bounties though: focus on finding bugs through controlled platforms like Juice Shop first. the world of bug bounty can be very discouraging for beginners, as progress is not guaranteed.
